TG Pen Test
TG Pen Test is our subscription-based recurring cybersecurity assessment service giving organizations the power to customize their desired cybersecurity assessment and delivery schedule.
What is TG Pen Test?
TG Pen Test is a subscription-based recurring cybersecurity assessment service that allows you to customize your desired assessment and delivery schedule. This service includes testing to assess the entire technical infrastructure of a business or enterprise, such as vulnerability assessments, penetration tests, application testing, cybersecurity control reviews, and more.
Why Your Organization Needs TG Pen Test
Organizations often perform once-a-year, costly penetration tests, usually for compliance or cyber insurance reasons. These types of tests can be helpful; however, they only provide a “point in time” status, which can lead to gaps in understanding what is happening from a trending perspective in the cybersecurity program. TG Pen Test aims to solve this by providing you with constant and actionable information about your cybersecurity program.
A subscription cybersecurity solution like TG Pen Test offers menu-based assessment selection and customizable delivery schedules for greater flexibility. The tailored testing schedule strategies are designed to achieve client-specific objectives.
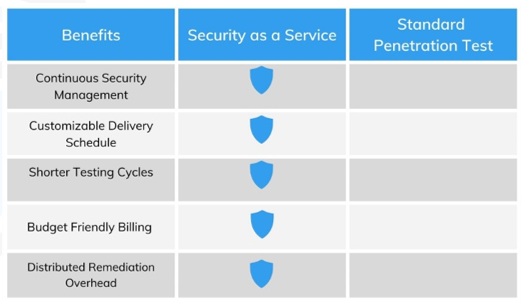
In addition, year-round cybersecurity assessments ensure awareness of current vulnerabilities and comprehensive attack surface coverage. You can rely on continuous cybersecurity management, shorter testing cycles, budget-friendly billing, and distributed remediation overhead, making TG Pen Test a cost-effective solution that doesn’t compromise your desired cybersecurity posture.
Why Security as a Service
“With services like TG Pen Test, we are able to customize reporting to fit our needs. Triden Group provides the expertise, and we know with Triden Group, the expertise will always be there.”
– Sr. Program Manager, Information Security, Global Golf Manufacture

What We Do
TG Pen-Test is a proprietary subscription-based solution for organizational cybersecurity provided by Triden Group. We collaborate with you in a series of pre-engagement sessions to map out the assessment schedule for the year, collect scope, prioritize client objectives for the program, authorize the rules of engagement, and configure and verify required environmental access.
Prior to each scheduled engagement window, we will connect with you to revalidate the collected data and access acquired during the planning phase. Once this is complete, we will execute the client-selected cybersecurity assessments and produce a report with an executive summary and strategic recommendation to address risks. The service is flexible, allowing you to swap assessments with similar work efforts for a specified engagement window and adjust to organizational challenges that may prevent on-time execution.
Our experts can:
Collaborate and develop a cybersecurity schedule for continuous year-round coverage.
Execute client-selected cybersecurity assessments with standardized testing methodology.
Create a report with high-level executive summary, strategic recommendations, and business intelligence views that identify vulnerability, remediation recommendations, and risk analysis.
Prioritize remediation recommendations within the context of the business and client-driven priorities or objectives.
Conduct remediation testing against previous assessment results to verify efforts.
Provide year-round access to cybersecurity experts for ongoing strategy.
Monthly and Quarterly Reports
Infrastructure / Network Penetration Testing
Wireless Penetration Testing
Web Application Penetration Test
API Penetration Test
Physical Penetration Test
Mobile Application Penetration Test
Cloud Control Review & Penetration Testing
Compliance Based Penetration Testing (PCI)
Segmentation Testing
One-time and Recurring Vulnerability Assessment
Remediation Validation Testing
Testing Methodologies
- NIST SP 800-115
- Penetration Testing Execution Standard (PTES)
- The Open Web Application Security project (OWASP)
- The Open-Source Security Testing Methodology (OSSTM)


